5 ways to improve your business cybersecurity

Cyber security is not something that can be easily achieved. With technology evolving, more and more businesses are struggling to prevent cyber-attacks.
Hackers never sleep, and new malicious tools and techniques are being devised daily and the protection of your business must be the number one priority.
When it comes to cybersecurity, you cannot only concentrate on protecting your “fortress”. This strategy may have worked in the past, but it’s definitely outdated. Businesses are not in a closed system. They are connected to customers, suppliers, employees, etc. via the Internet 24 hours a day, 7 days a week which means that they are exposed to cyberattacks all the time. Regardless of that many businesses out there are still spending around 87% of their security budgets on firewall technologies, according to Tim Grieveson, chief cyber strategist at Hewlett-Packard.
Unfortunately, there is no recipe for dealing with hacking at 100%, but there are steps any business can take to significantly improve its security and protect against data leakages.
Table of Contents
Knowing your data
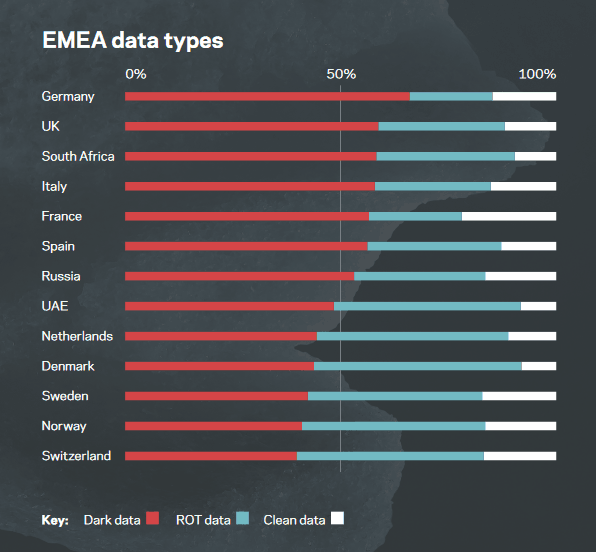
Many businesses have their data spread everywhere. Every single device in their IT system has a bit of data stored. A survey made by Veritas shows that UK businesses have stored 59% of data classified as ‘dark data’.
View the full report here.
Every cybersecurity strategy starting point is the data your business has. How can you protect your data if you don’t know how much and what data exactly is there?
Data encryption
After knowing your data, you can use one of the best practices in data protection – data encryption along with managing encryption keys. When the data is encrypted it becomes useless for the hackers.
Multi-factor authentication (MFA)
There are people behind every business. People always forget or lose their passwords and even worse – they create weak passwords. A weak password means weak security for business data.
The Multi-factor authentication (MFA) is a really easy process which gives you the extra security your business needs. It is a security system that requires more than one method of authentication from independent categories of credentials to verify the user’s identity for a login or other transaction. Besides the reliability and security this method gives, it’s also a really flexible mthod because people within the company can access the business data from everywhere at any time.
Cybersecurity from the insight
Hackers are really smart and as we said above – malicious tools and techniques are being devised daily. Have you heard about SPAM and Phishing? That’s right these are the hidden threats in every email and people just love clicking on links and attachments in their emails without checking if they are coming from a trusted sender.
One of the top priorities for every business should be to educate the staff about this kind of threats. You can read more on how to recognise malicious emails:
How to protect yourself and your business from SPAM and Phishing emails (PART 1)
How to protect yourself and your business from SPAM and Phishing emails (PART 2)
Increase the control
If your employees use their own mobile devices for work purposes the IT team should at least restrict the access to all sensitive data within the company.
“Organisations need to embrace a zero-trust philosophy,” says Jason Garbis from Cryptzone and we cannot agree more.
Hackers are waiting behind every corner, so businesses must take extra care for all of their data, especially for the sensitive information.
Cybersecurity isn’t something that you can just ignore. Your business needs to be protected 24/7 and this is not a job only for your IT team but for everyone within the company.
Did you know that Private Cloud technology combines each of these best practices and many more to protect businesses’ data? Contact us and our experts will explain everything you need to know!


