How to protect yourself and your business
from SPAM and Phishing emails? (PART 1)

Nowadays the cyber-security has become one of the most important aspects when speaking about online presence. It is essential for individuals and business professionals to know how to recognise Spam emails and protect themselves and their data.
Spam and malicious email practices have been around for some time already, but still, there are many people who fall victims to them. Cyber-criminals are becoming quite savvy in luring people in and getting them to open emails, click on links, and download attachments.
We believe that safety comes first when speaking about IT. Therefore, we decided to share some useful information, based on our expertise, about the latest developments of Spam and Phishing email practices, tips on how to protect yourself, and finally – how businesses can benefit from cloud-based spam filtering solutions.
In the desire to give as much information as possible but at the same time not to bore you with long articles 🙂 , we divided the whole article into three parts. Enjoy reading!
Table of Contents
What is SPAM?
Spam is the equivalent to the annoying junk mail people used to get in their post boxes but in an electronic version. The Spam email messages are not only annoying but can be dangerous if they are part of a phishing scam.
Usually, Spam emails are sent in massive quantities from online criminals to:
- Make money from the recipients who open the email;
- Run scams/ phishing emails by obtaining credit card or bank details or passwords;
- Spread malicious code onto computers;
- Extract money through blackmail
Ways to reduce SPAM
Report It – Most email clients have the option to mark an email as Spam. This will prevent the messages from being delivered to the inbox.
Filter it out – Enable the filters of your email program but don’t forget to check the junk folder for emails you may want.
We, as professionals, would recommend you to use Microsoft Office 365. The process of reviewing emails which have been detected as spam, but you actually need, is really simplified. Office 365 allows you to set up quarantine for the incoming messages that have been filtered as spam, for later review.
Be responsible – Take responsibility for your online presence and hide your email address from social media profiles and other public accounts.
What is Phishing?
Phishing is a way online criminals use to trick people into sharing their financial or personal data. They are known also as Scam emails. Phishing messages usually look very legitimate coming from businesses, institutions such as telecoms, banks etc. Phishing attacks can also use malicious websites and email to infect your machine with viruses and malware.
Some of the Phishing emails can be easily recognised by your email provider and will be automatically filtered into the spam folder. But the problem is that some of the malicious emails won`t be captured, so it’s important for you to know how to recognise them in order to protect yourself.
How do the SPAM/ Phishing emails look like?
Every day we get tons of emails (more than 60% of them are Spam), but do we recognise which are the “tricky” ones?
Usually, the email servers detect Spam emails by using spam filter software. In most cases, they prevent them to reach your inbox. The problem is that the cyber-criminals invent new ways to “deceive” this software every day.
Here is an example of how a SPAM/Phishing email can look exactly as an ordinary non-spam email we receive daily:
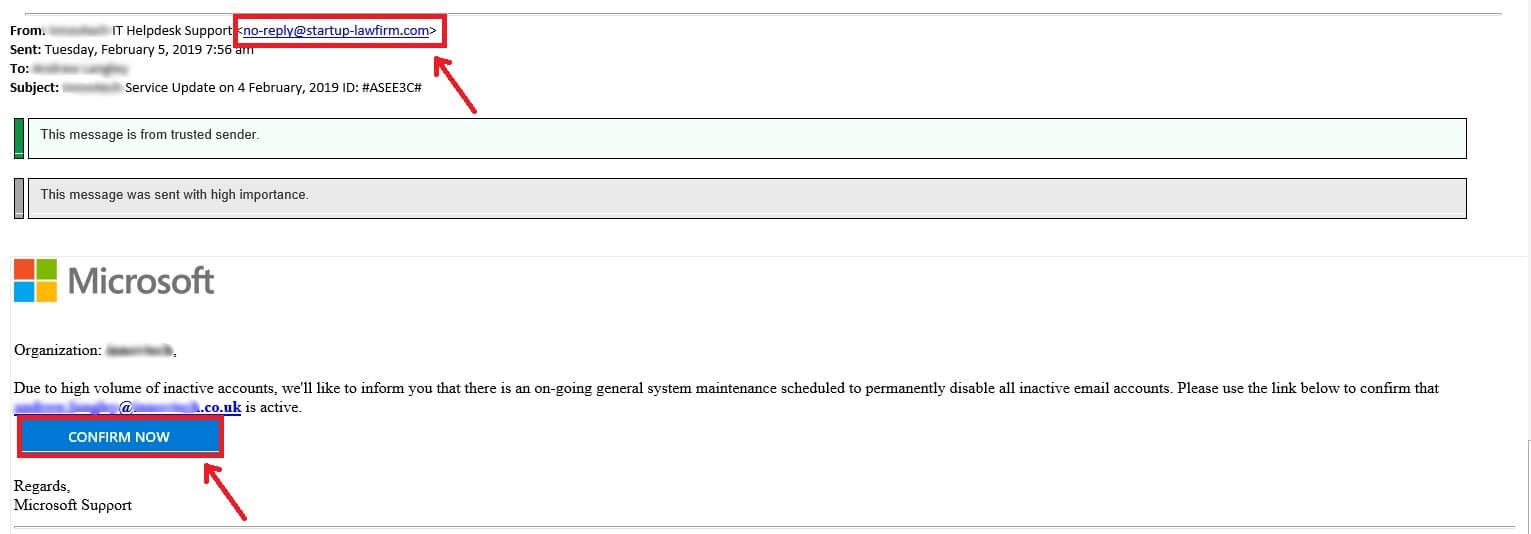
- The first “not-trustable” thing that we notice is the email address from which is sent – “no-reply@startup-lawfirm.com”
- The second thing is the big blue button “Confirm now” which looks alright at first, but when you actually hover over it shows the exact link of where is going to forward you – “https://sanctus.link/kuld/?email=your name@company.co.uk”
TIP: The first thing you can check when you get this type of email is the sender’s email address. With the slightest doubt – do not click any links in the message. As it is shown in the above example – it is obvious that this is not a Microsoft email address.
However, in many cases, the sender’s email address can look legitimate and the best thing you can do is to contact your service provider, who will further investigate the email address legitimacy for you.
Do you like the article until now? In the next part, we will give you more real-life examples and advises how to recognise malicious mail and protect yourself and your business.


